Hardware & Devices

Is there a recommended method to dispose used IT equipment?
Hardware or IT equipment as you commonly call it are part of your digital assets. IT equipment have various categories like mobile phones, laptops, desktop computers, servers, switches, routers etc. These may be used for personal use or used within an organization for business purposes. Due to a failure in the device or a requirement to upgrade the hardware at some point in time you need to dispose the IT equipment. Disposing the hardware may not be straightforward as it seems because it is not just the hardware, we are disposing but the sensitive information contained within the devices. This sensitive information may be financial data, customer information, company secrets and these information needs to be securely disposed.
The information contained in the device that is going to be disposed may be important for you. This is the reason why you should backup the data in your device. Backup the data to an external hard drive or a cloud storage whichever is suitable depending on the situation.
Carrying out a Factory reset on your mobile phone will erase all the data on your phone. This may include contacts, pictures, videos, documents and anything else. If you plan to resell or give the used mobile phone to someone it is a recommended practice to implement a factory reset on the phone. Always be mindful to backup your contacts and other useful information to a cloud storage like Apple or Google to recover the useful information or import it to your new phone. The way to carry out a factory reset may differ depending on the make and model of the mobile phone you have. However the following steps show the factory reset of an Android mobile phone.
- Tap the Settings icon from your home screen or app drawer
- Swipe up to scroll down to the bottom of the settings menu
- Tap System
- Hit Reset options
- Select Erase all data (factory reset)
- Swipe up to scroll down to the bottom of the page
- Hit the Reset phone button
- Enter your device PIN and select Continue
- Select Erase everything
- Your phone will reboot and you'll have to go through the setup process again before you're able to restore your data
Due to replacement or upgrade of the laptop, desktop or server you may want to dispose the device. If your company is under strict regulation or standard that your sensitive information must be disposed securely you may need to use some software to wipe the hard drives before they are disposed. There are open source as well as commercial software that can be used for this purpose.
This is an open source software utility that can help to erase the hard drive. Darik's Boot and Nuke ("DBAN") is a self-contained boot image that securely wipes the hard disks of most computers. DBAN is appropriate for bulk or emergency data destruction.
You may download this using the following link.
https://sourceforge.net/projects/dban
This is a commercial tool and much more advanced than DBAN. Supports SSD drives as well. Provides digitally signed certificate of proof of erasure for audit trail purposes.
You may get more information from the following link.
https://dban.org/blancco-drive-eraser
Exposing the hard drive to a strong magnetic field will sanitize the data. This will destroy the data in the hard disk.
These are specialized equipment used to shred the hard drive into small chunks.
Using an industrial drill to punch holes in the hard drive to destroy any data contained within the hard drive.
This is also an option to get rid of the information on the hard disk.
Sometimes used IT equipment are called as e-waste due to the electronic components within them. They can be reused or recycled depending the requirement of the owner.
https://brightlineit.com/dispose-of-old-computers-company-hardware
What is BYOD?
Advancements in computing has resulted in novel, portable and convenient devices which allow a user to interact with various IT related services and platforms. In parallel to developments in computing domain, wireless communication technologies and infrastructure have evolved at a rapid rate during the past 10 years. Inevitably, the combination of device portability and highspeed mobile data access have forced organizations to adapt and allow employees to use their personal devices within company premises and beyond.
Bring Your Own Device (BYOD) concept allows employees to utilize their personally owned IT resources such as laptops and mobile phones to carry out corporate activities. In order to conduct daily business functions and to gain access to corporate information employees connect their personal devices to company network. This enables employees to be extremely flexible in business related activities by utilizing any endpoint device independent of time and location. One of the biggest attractions of BYOD is the substantial reduction of purchasing and operational cost related to devices. Surveys conducted around the world clearly indicate that there is an increase of employee satisfaction with respect to BYOD and it is playing an integral part in shaping organizations device usage policies. Many respondents for these surveys continually point out that getting to use a device they are more comfortable with could lead to a significant increase in overall productivity.
Inherently BYOD allows an employee to distort the conventional boundaries of personal life and workplace. Combination of device capabilities such as 4G and network access solutions such as VPNs allow users to engage with the workplace after traditional work hours. This results in an evident increase in responsiveness towards the business functions and overall productivity. Hence facilitating a BYOD friendly work environment has become one of the top priorities of a CIO.
However, if not governed properly BYOD can quickly turn in to a nightmare for organizations. Inadequate governance and security may result in catastrophic outcomes for organizations which could outweigh all the benefits stated above. Because the users personally owned devices are most likely to be vulnerable against various types of attacks, proper security solutions should be implemented before BYOD is turned into an inherent part of the organization’s IT ecosystems. According to SANS Mobility/BYOD Security Survey, 49% of the respondents (security analysts, CIOs and CISOs) believe that their current policies around BYOD barely caught the basic concerns of enterprise security requirements[1]. Although data confidentiality and integrity are traditionally earmarked as main security concerns with respect to BYOD, alarming rise of cryptographic ransomware is now affecting system and resource availability of businesses around the world.
Organizations around the world are now warming up to the security risks of BYOD. Consequently, we are seeing companies establishing comprehensive security and compliance policies to support mobility and BYOD requirements. Preparing and imposing these policies is not as straightforward as one may believe. The biggest concern with BYOD is that the device and its apps do not belong to the organization. Hence, legally and policy wise the question beckons, is the company allowed to have full control over an employee’s personal device? Albeit it is for security reasons. With so many complexities involved in BYOD policy development, laying an impermeable security blanket to satisfy organizational requirements require intricate and meticulous planning.
K. Johnson, “ANS Mobility/BYOD Security Survey”, SANS Analyst Program, 2018, The SANS Institute, Maryland, USA.
How can the business network be secured?
- Change default settings before deploying on production network.
- Update firmware to the latest update before deploying the device into the production network.
- Remove all non-essential services and programs. Close all unused ports.
- Implement “Least Privilege” on user accounts and limit the users.
- Enable Logging and auditing. Running activity reports of the devices to detect unusual activities. Eg: failed login attempts.
- Ensure that device is configured to use Secure Protocols. SSH rather than telnet connections.
- Use VLAN techniques segregate the internal network.
- Have a DMZ network to place the web server or other services accessed by outsiders.
- Micro segment the network in datacenter.
- Implement a firewall to control traffic among networks.
- Implement IPS / IDS to detect and block malicious traffic at the perimeter.
- Changing the SSID or Masking it.
- Turning On Encryption in the Wireless Access Points. Most preferable is WPA2.
- Changing Encryption Keys/Passwords from the Default Settings.
- Implement Radius server to authenticate users in to wireless network. Using Two Factor or Better Authentication.
- Setting up a schedule for changing wireless network name and passwords
- Performing regular backups of the device configuration.
- Implement network monitoring tools. Deploy a SIEM tool to correlate all logs gathered throughout the network.
- Acquire services of a SOC.
- Vulnerability assessment on servers and network devices.
- Check for unused or unnecessary applications running in the background of client PCs and servers, uninstall them.
- Review network ports open in servers and client PCs, close all unnecessary ports.
- Review the settings of the firewall including the rule base. Identify outdated rules which no longer servers and remove them. Inquire about the new requirements of the network and implement suitable rules or modify existing rules.
- Configuration and signature patch level of Anti-virus/anti-malware software.
- The overall health of servers, software, and applications
- Evaluate the Backups by performing restore test.
- Review if the network architecture is aligning with business strategy and security. Perform penetration testing verify controls are effective.
- Make Sure Your Employees Are Aware of Online Risks. Holding Formal Cybersecurity Training Sessions.
- Sending Out Security Updates and Resources.
- Actively Testing Your Employees by Creating Fake Phishing Emails.
- Implementing IT security policies on Strong Password Guidelines and acceptable use of internet based resources.
What are the steps to be taken if there is a PBX Fraud?
Has your business been charged with exorbitantly high phone bills without any rhyme or reason? Be aware, you could be exploited by criminals by committing a Private Branch Exchange [PBX] or a dial through fraud where telephone systems are hacked into allowing calls to be routed through the system to high rate international/premium rate numbers.
These types of attacks generally continue over a significant period of time as most companies are unaware of such threats resulting in inflicting substantial financial damages to businesses. In most instances, voice over IP (VOIP) telephony, systems are compromised by malware or accessing an IP address connected with the PBX box to bypass the company’s firewalls.
How do I prevent PBX Frauds?
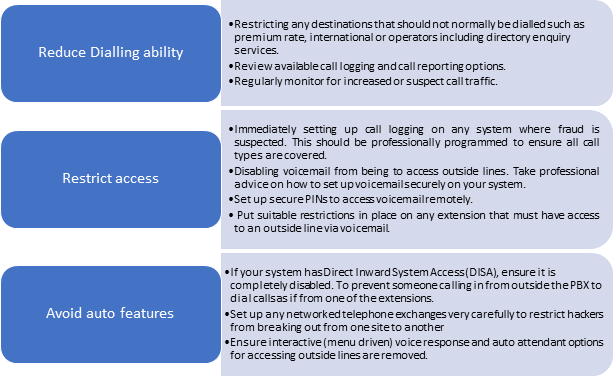
- Be sure to take steps to ensure both the physical and technical security of your equipment.
- Seek advice from your system or managed service provider to help you secure your system. Some service providers have precautions in place such as monitoring unusual usage spikes, cutting off services if they exceed pre-agreed thresholds or disconnection in the event of their SIMs are connected to a computer, switchboard or the internet.





 Total Users : 228467
Total Users : 228467